Perspectives
Regional Security at the Brink: U.S. Distributed Footprint, Security Partnerships and Sovereignty Trade-Offs in Post-Niger West Africa
This paper by academic and retired Ghana army chief, Colonel Festus Aboagye, provides a comprehensive analysis of the U.S. military’s strategic repositioning across West Africa following the forced withdrawal from Niger in August 2024. Examining the December 2025 airstrikes in Sokoto, Nigeria, it documents the emergence of a so-called distributed “light footprint” model spanning Ghana, Benin, Côte d’Ivoire, and Chad—and assesses the sovereignty implications of this novel security architecture.
Colonel Festus Aboagye (Retired)
28 December 2025
Abstract
The December 2025 U.S. airstrikes in Sokoto, Nigeria, mark a critical inflexion point in West African security architecture. Following its expulsion from Niger, Washington has deployed a distributed “light footprint” across Ghana, Benin, Côte d’Ivoire, and Chad—a novel operational model that reduces coup vulnerability while increasing regional dependency. This paper documents three converging dynamics: 1) the shift from advisory support to direct kinetic intervention, justified through instrumentalised religious persecution narratives that obscure multifaceted governance failures; 2) Nigeria’s acceptance of foreign strikes despite sovereignty costs, reflecting capability gaps in precision airpower; and 3) the emergence of asymmetric security dependencies that risk entrenching external military presence under a humanitarian guise. Drawing on operational analysis and threat assessment, the paper proposes five African Union institutional mechanisms—from post-strike accountability protocols to continental drone policies—designed to reassert African agency before externalised counterterrorism becomes the irreversible norm.
I. Introduction
On Christmas Day 2025, the United States (U.S.) conducted a series of significant airstrikes against Islamic State targets in Sokoto State, northwestern Nigeria, representing a marked escalation in U.S. military involvement in West Africa.
This paper aims to sound an early strategic warning by critically analysing the shift toward foreign kinetic intervention in West Africa, the instrumentalisation of religious narratives in counterterrorism, and the emergence of a distributed external military footprint, and assessing how these dynamics risk undermining sovereignty, inflaming sectarian tensions, and entrenching neocolonial security dependency.
II. Operational Overview
The strikes targeted two ISIS encampments in Sokoto State, within the Bauni forest in Tangaza local government area, specifically linked to the Islamic State-Sahel Province (ISSP), sometimes known locally as “Lakurawa”. U.S. Africa Command (AFRICOM) characterised the strikes as “deadly”, reporting that they killed “multiple ISIS terrorists” with no confirmed civilian casualties as of December 26. Any subsequent acknowledgement of civilian fatalities will likely heighten opposition to the U.S. engagement in Nigeria.
To understand why these strikes represent a strategic escalation rather than routine counterterrorism, it is essential to examine the threat landscape that prompted direct U.S. kinetic action.
III. The ISSP/Lakurawa Threat: Strategic Context
ISSP militants, sometimes operating under the name “Lakurawa”, are part of long-established networks that have expanded from Niger’s Dosso region into northwestern Nigeria’s Sokoto and Kebbi states. Active since approximately 2017, these armed fighters—primarily from the Fulani pastoral ethnic group—were initially invited by Sokoto traditional authorities to protect communities from bandit groups, but “overstayed their welcome, clashing with community leaders and enforcing a harsh interpretation of Sharia law.
ISSP became more active in Nigeria’s border communities after Niger’s July 2023 military coup, which fractured cross-border military cooperation. Empirically, ISSP has maintained a low profile, operating covertly to infiltrate and entrench itself along the Niger-Nigeria border while expanding toward Benin. Politically motivated violence in border regions, including Dosso (Niger), Alibori (Benin), and Sokoto-Kebbi (Nigeria), has more than doubled since 2023.
This escalating violence is not confined to border security metrics—it carries profound symbolic and strategic dimensions that extend far beyond immediate counterterrorism objectives.
A critical question remains unaddressed: would Nigerian sovereignty be better served by rejecting external intervention and accepting slower, indigenous responses—even if this allows ISSP to consolidate territorial control in the interim? While the answer depends on whether one prioritises short-term operational gains or long-term strategic autonomy, the Tinubu administration’s calculus clearly favoured immediate capability supplementation over purist sovereignty principles.
IV. Strategic Significance and Regional Spillover
Sokoto’s selection as a strike target carries symbolic weight beyond counterterrorism: the historic Sokoto Caliphate, responsible for spreading Islam into Nigeria, remains revered by Nigerian Muslims, making operations here extremely sensitive. Throughout 2025, Jama’at Nusrat al-Islam wal-Muslimin (JNIM) and ISSP further entrenched their presence in the Benin-Niger-Nigeria tri-border area, transforming previously distinct Sahelian and Nigerian theatres into a single, interconnected conflict environment stretching from Mali to western Nigeria.
The security crisis is fundamentally a governance problem, with militants exploiting the near absence of state presence in conflict hotspots—areas with some of Nigeria’s highest levels of poverty, hunger, and unemployment. While Nigerian military airstrikes target militant hideouts, operations are not usually sustained, and militants easily relocate through vast forests connecting several northern states.
This context clarifies why U.S. intervention occurred: ISSP represents a transnational jihadist expansion exploiting governance vacuums and coup-induced security disruptions. However, it raises fundamental questions about whether kinetic strikes address underlying governance and development deficits, or whether such interventions risk becoming perpetual responses to symptoms rather than causes.
V. Political Context: Coordination and Competing Narratives
Understanding the threat context alone, however, does not explain the most problematic dimension of the December 25 strikes: the stark divergence between how the U.S. and Nigeria framed the operation’s purpose and justification.
Joint Operations and Diplomatic Coordination
In the immediate aftermath, President Trump’s announcement emphasised unilateral resolve. However, both the Pentagon and the Nigerian Foreign Ministry quickly confirmed the strikes were a joint operation, with two direct conversations between Nigerian Foreign Minister Yusuf Tuggar and U.S. Secretary of State Marco Rubio on the day of the strikes to coordinate intelligence.
The “Religious Freedom” Framing and Its Contradictions
The most distinctive feature of the strikes was the conflicting U.S. vs Nigeria narrative framing:
- U.S. Perspective: Presidential rhetoric characterised the strikes as a direct response to the “slaughter of Christians”, claimed to be occurring at “levels not seen for centuries”. This followed the October 2025 redesignation of Nigeria as a “Country of Particular Concern” for religious freedom and Trump’s November ultimatum threatening to go in “guns-a-blazing” if Nigeria failed to protect Christian communities.
- Nigerian Perspective: The Nigerian government and independent analysts emphasise that violence in the North-West is multifaceted, affecting both Christians and Muslims, with Muslims often constituting the majority of victims in Muslim-majority northern regions. Table 1 shows the narrative contestation matrix: security vs religious framing by the U.S. and Nigeria.
| External Narrative (U.S.) | Local / Regional Reality |
|---|---|
| Protection of Christians: Framed as a religious persecution response | Multi-actor Insecurity: Complex violence affecting all communities |
| Moral urgency: “Slaughter at levels not seen for centuries” | Criminal–terrorist hybrid violence: Both Christians and Muslims were victimised |
| Counterterrorism: Part of the global “Peace Through Strength” | Governance failure: Security overstretch and state weakness |
| External Legitimacy: Unilateral resolve with coordinated action | Sovereignty sensitivity: Pragmatic but delicate acceptance of intervention |
The religious framing by the U.S. risks inflaming sectarian tensions and providing extremist groups with recruitment propaganda, while potentially obscuring the multifaceted nature of regional insecurity.
Nigerian Domestic Calculations
President Tinubu faces mounting pressure to demonstrate security progress, with over 10,200 deaths from armed group attacks and 12,290 abductions generating ₦13 billion (about US$9 million) in ransom demands during his first two years. The deteriorating situation—which saw the North-Central zone overtake the Northeast as Nigeria’s new epicentre of violence and prompted a sweeping military reshuffle in October 2025—has severely tested his administration’s credibility on its core “Renewed Hope” security agenda.
Nigeria’s 3-Phase Drone/UAS Acquisition
The strikes reflect pragmatic calculations about capability gaps despite modernisation efforts. Nigeria’s unmanned aerial capability has developed through three distinct phases (see Table 2 below). In Phase 1 (2014–2020), China anchored Nigeria’s entry into armed drones with the CH-3A (2014), later expanding MALE and UCAV capacity through Wing Loong II and CH-4 systems, establishing persistent ISR and strike capabilities for counter-insurgency operations. During phase 2 (2022–2023), Türkiye drove diversification with Bayraktar TB2s and tactical systems (Songar, TOGAN, BAHA), creating a layered drone mix combining long-endurance strike platforms with flexible short-range assets. Phase 3 (2018–2025) saw the emergence of indigenous development with the Tsaigumi ISR drone (2018), culminating in the public debut of a locally produced attack drone (2025); these signalled ambitions to reduce external dependence.
| Year | System/Type | Origin | Status | Notes |
|---|---|---|---|---|
| 2006-07 | Aerostar (ISR) | Israel | Acquired | First operational UAV fleet; 9 units |
| 2014 | CH-3A (UCAV) | China | Delivered | Used in strike roles against insurgents |
| 2016 | Yabhon Flash-20 | UAE | Reported | Acquisition disclosed 2016 |
| 2018 | Tsaigumi (ISR) | Nigeria | Inducted | Indigenous platform (AFIT + UAVision) |
| 2020 | Wing Loong II (UCAV) | China | Disclosed | NAF confirmed acquisition Nov 2020 |
| 2020-21 | CH-4/CH-4B (UCAV) | China | Ordered | Expected delivery late 2021 |
| 2021 | Aerosonde Mk 4.7 (ISR) | USA | Contracted | DoD contract completed Sept 2021 |
| 2022 | Bayraktar TB2 (UCAV) | Türkiye | Acquired | Operational by Sept 2022 |
| 2022 | Songar (armed rotary) | Türkiye | Acquired | Fleet expansion noted |
| 2023 | Wing Loong II (additional) | China | Sighted | Multiple airframes observed at NAF facilities |
| 2023 | TOGAN/BAHA (tactical ISR) | Türkiye | Delivered | Export to security forces Aug 2023 |
| 2025 | Indigenous attack drone | Nigeria | Debuted | Publicly showcased April–Nov 2025 |
Nigeria’s UAV Capability Mix
Despite this diversified acquisition timeline, Nigeria’s operational UAV ecosystem remains constrained by strategic dependencies. Table 3 categorises Nigeria’s current unmanned capabilities by function, revealing a capability structure heavily reliant on external suppliers despite indigenous development efforts.
| Category | Primary Systems | Role | Operational Significance |
|---|---|---|---|
| ISR-only UAVs | Aerostar (Israel); Tsaigumi (Nigeria); BAHA (Türkiye) | Surveillance, target acquisition, border monitoring | Foundation of situational awareness; supports both air and ground operations |
| Armed Multirotor / Tactical UAVs | Songar (Türkiye) | Close-range strike, urban and counter-insurgency support | Precision effects at tactical level; suited for internal security operations |
| MALE / UCAV Platforms | CH-3A; Wing Loong II; CH-4 (China); Bayraktar TB2 (Türkiye) | Persistent ISR, precision strike, counterterrorism | Strategic enablers; substitute for manned airpower in permissive environments |
The “Targeting Circuit” Bottleneck: Why Nigeria Could Not Act Alone
NAF’s inability to neutralise the Sokoto targets independently, despite possessing an inventory of Chinese (CH-4) and Turkish Bayraktar (TB2) drones, reveals critical technological and intelligence bottlenecks. This deficit in precision airpower drives a profound asymmetric security dependency on the U.S. The “crucial question” of why Nigeria required U.S. kinetic intervention lies in three areas of efficacy:
- Sensor Resolution and “Fused” Intelligence: While Nigeria’s Turkish and Chinese platforms provide battlefield-grade electro-optical/infrared (EO/IR) imagery, they often lack the Multi-Spectral Targeting System (MTS-B) found on the U.S. MQ-9 Reaper. The MTS-B offers an “ID Card” resolution standard, capable of identifying high-value targets (HVTs) by facial features or specific clothing from extreme altitudes where the drone remains invisible. Furthermore, Nigeria’s “targeting circuit” for its existing fleet is essentially a “closed loop” where pilots rely on immediate visual feeds. In contrast, the U.S. provides a “fused” intelligence architecture, where live drone data is analysed in real-time by a global network of specialists who cross-reference it with signals intelligence (SIGINT) to confirm identities in complex civilian environments.
- Munition Precision–Hellfire vs. MAM-L: The choice of munition represents a vital sovereignty trade-off. The U.S. AGM-114 Hellfire—specifically its Low Collateral Damage (LCD) variants like the R9X—is engineered for “surgical” strikes with a highly focused blast radius. Conversely, the Chinese AR-1 and Turkish MAM-L munitions in Nigeria’s arsenal are generally designed for open warfare with higher explosive yields. For the Sokoto strikes occurring near civilian clusters, the Nigerian government likely assessed that its own munitions carried an unacceptable risk of “collateral tragedies,” similar to previous accidental NAF strikes.
- The “Legal and Political” Shield: Beyond hardware, the use of U.S. platforms serves as an “Accountability Outsourcing” mechanism. By utilising U.S. targeting oversight, the Tinubu administration can claim that the operation met international “gold standards” for civilian protection, providing political insurance against the domestic fallout of a botched strike. As detailed in Table 4, this reliance is fundamentally a product of the efficacy gap between U.S. and regional systems, where the MQ-9 Reaper’s superior sensor resolution and surgical munition choices provide a level of precision currently unavailable to Nigeria’s indigenous or existing foreign fleet.
| Feature | U.S. MQ-9 Reaper | Turkish TB2 / Chinese Wing Loong |
|---|---|---|
| Primary Sensor | MTS-B (Ultra-high resolution) | Standard EO/IR (Battlefield grade) |
| Munition Choice | Hellfire (Specific LCD variants) | MAM-L / AR-1 (General-purpose explosive) |
| Intelligence Loop | Global “fused” network | Localised “pilot-in-the-loop” |
| Mission Profile | Surgical HVT elimination | Tactical battlefield support |
These competing narratives and domestic calculations reflect more profound strategic shifts in U.S.-Africa security relations that extend well beyond Nigeria’s immediate counterterrorism needs. The strategic shifts manifest most visibly in the U.S. military’s geographic repositioning across West Africa. Table 5 summarises the four critical dimensions of strategic transformation signalled by the Sokoto strikes:
| Factor | Assessment |
|---|---|
| Shift in Engagement | Marks a transition from “advise and assist” to direct kinetic action in the Nigerian theatre. |
| Regional Expansion | By striking in Sokoto (North-West) rather than the traditional Islamic State West Africa Province (ISWAP) stronghold in the North-East (Borno), the U.S. acknowledges the spread of IS-affiliated groups toward the Sahel/Niger border. |
| Sovereignty vs. Necessity | Nigerian government approval suggests pragmatic, if delicate, acceptance of U.S. airpower to compensate for domestic security overstretch. |
| Global Context | Occurring a week after similar U.S. operations in Syria, these strikes may reflect a broader “Peace Through Strength” campaign to degrade ISIS global affiliates simultaneously. |
VI. The New U.S. Military Footprint: From Centralised to Distributed
Strategic Rationale for Redistribution
Following Niger’s July 2023 coup and the August 2024 forced withdrawal, the U.S. abandoned its centralised model—anchored by massive desert bases like Air Base 201—in favour of a distributed “light footprint” strategy across multiple coastal West African nations. This approach reduces vulnerability to single-country political upheaval, though it increases drone flight times to Sahel targets.
Current Operational Locations (Late 2025)
Personnel and heavy equipment from Niger’s former Air Base 101 and 201 were initially consolidated at U.S. facilities in Germany and Italy before redistribution. By late 2025, U.S. counterterrorism operations span four main locations:
- Ghana: Primary operational hub, with intelligence flights and strikes launched from Accra’s Kotoka International Airport and potentially Tamale Air Force Base in the north.
- Benin: Forward surveillance site, where Washington invested $4 million to upgrade a northern airfield (near Parakou or Karimama) for reconnaissance missions, helicopter operations, and Special Forces border security training.
- Côte d’Ivoire: Strategic pivot point, with ongoing 2025 negotiations to establish drone deployments from existing military infrastructure in Abidjan and northwestern sites near Odienné, close to the Mali and Guinea borders.
- Chad: Maintains northern surveillance capabilities through special operations forces who returned to N’Djamena in late 2024, following a brief earlier withdrawal.
While this distributed model offers tactical flexibility, it introduces systemic risks that extend beyond immediate operational concerns. To contextualise this emerging architecture, Table 6 situates the U.S. distributed footprint within the broader spectrum of contemporary security partnership models operating across Africa, highlighting the distinctive sovereignty trade-offs inherent in each approach.
| Security Partnership Model | Example | Sovereignty Trade-off |
|---|---|---|
| Full Basing Rights | Djibouti (U.S./China/France) | High presence, long-term commitment |
| Distributed Light Footprint | West Africa 2025 | Lower visibility, uncertain commitment |
| Equipment/Training Only | U.S.-Tunisia | Minimal presence, capacity gaps remain |
| Regional Force (African-led) | AMISOM/ATMIS/AUSSOM | Higher ownership, chronic underfunding |
VII. Risks and Implications
While this distributed architecture offers operational advantages in a politically unstable region, it generates four categories of risk that African policymakers and continental institutions must urgently address.
Extremist Recruitment and Propaganda
Foreign intervention, particularly when framed in religious terms, provides extremist groups with recruitment material to portray conflicts as a “Crusade” against Islam. ISSP and other terrorist networks in Nigeria, coastal Guinea countries, and the MENA region may escalate operations in response.
Sectarian Tensions
The U.S. emphasis on “protecting Christians” within the broader “global war on terror” narrative risks inflaming existing religious tensions within Nigeria’s diverse population and beyond, absent balanced local diplomacy.
Uncertain Long-Term Commitment
Defence Secretary Pete Hegseth’s “more to come” comment suggests sustained operations in Nigeria, coastal Guinea areas, and the Sahel. However, a critical dilemma persists: counterterrorism in a region that may not be a top U.S. strategic priority offers no guarantee of long-term engagement, potentially leaving African partners vulnerable to abandonment.
Asymmetric Security Dependencies
Recent West African developments carry a long-term risk of creating asymmetric security dependencies that erode strategic autonomy by outsourcing regional security to competing global powers pursuing strategic containment policies that may not align with African sovereignty and stability. It is permissible to conclude that, without a genuine partnership that respects African agency, these dynamics could lead to a long-term erosion of sovereignty. The danger is that the “regional security” narrative becomes a convenient vehicle for external powers to maintain a military presence that serves their geopolitical interests under the guise of collaborative security and humanitarian protection.
These risks—ranging from extremist recruitment to sovereignty erosion—are not hypothetical future scenarios. They are already materialising in the immediate aftermath of the Sokoto strikes, demanding urgent strategic reflection on the path forward.
VIII. Conclusion
The Christmas Day 2025 airstrikes in Sokoto State mark a pivotal moment in U.S.-Africa security relations, signalling Washington’s transition from advisory support to direct kinetic intervention in Nigeria’s counterterrorism landscape. While operationally coordinated between both governments, the strikes reveal a troubling divergence in narrative framing: the U.S. administration’s emphasis on religious persecution conflicts with Nigeria’s understanding of the violence as a complex, multifaceted security crisis affecting communities across religious lines.
The shift to a distributed military footprint across Ghana, Benin, Côte d’Ivoire, and Chad demonstrates strategic adaptation following the Niger withdrawal. Yet it also represents a broader recalibration of Western engagement in the region. This decentralised approach, while reducing vulnerability to single-country political instability, raises fundamental questions about sovereignty, sustained commitment, and the risk of inadvertently fuelling the very extremism it seeks to combat through religiously charged rhetoric that terrorist groups can exploit for recruitment.
Most critically, these developments risk establishing a troubling precedent: the gradual outsourcing of regional security to external powers pursuing containment strategies that may not align with Africa’s long-term stability interests. Without careful diplomatic management, balanced local engagement, and genuine partnership that respects African agency, current counterterrorism efforts could inadvertently serve neocolonial dynamics rather than sustainable peace. The international community must remain vigilant that the “regional security” narrative does not become a vehicle for undermining African sovereignty under the guise of protecting lives. This is the challenge for the African Union and African regional organisations.
Meeting this challenge requires moving beyond declaratory statements to concrete institutional mechanisms. The following policy recommendations provide an actionable framework for the AU Peace and Security Council to reassert continental agency in the face of externalised security interventions.
IX. Recommendations
To address the concerns of sovereignty, neocolonial dependency, and narrative imposition following the U.S. airstrikes in Nigeria, the AU must transition from reactive diplomacy to proactive institutional oversight. The strategic landscape in late 2025 makes it imperative that the AU Peace and Security Council (PSC) consider the following policy recommendations.
- Establish Continental Oversight of Foreign Kinetic Action: The AU should require that any foreign military strike on member-state territory—regardless of host-state consent—be formally notified to the AU PSC within 24-72 hours, supported by a standardised Post-Strike Accountability Brief covering civilian impact, intelligence justification, and legal basis under AU norms. The purpose is to prevent bilateral security arrangements from bypassing and undermining continental transparency and non-indifference principles. However, the AU will have no enforcement mechanism against major powers that ignore this requirement.
- Counter-Narrative Weaponisation through African Analysis: Mandate the African Centre for the Study and Research on Terrorism (ACSRT) to issue an independent Threat Context Report following any major external intervention in Africa. This will anchor counterterrorism narratives in African-led analysis and prevent the reduction of complex conflicts into sectarian or ideological propaganda.
- Regulate Distributed Foreign Military Footprints: Develop an AU Continental Drone and Surveillance Policy setting clear limits on the scope, duration, basing, and authorisation of foreign unmanned aerial vehicles (UAVs) and intelligence, surveillance and reconnaissance (ISR) operations on African soil. The purpose is to prevent the gradual entrenchment of coastal states as permanent launch platforms for external military operations outside a collective AU strategy.
- Reinvigorate the ASF for Sahelian Security: Fast-track the reconceptualisation of the African Standby Force (ASF) to incorporate a counterterrorism capability, to close critical regional capability gaps and reduce reliance on foreign airpower. After more than 20 years of chronic underfunding and lack of full operationalisation, why would the ASF change now?
- Mediate the AU–Sahel Divide: Convene a high-level AU-led Sahel Reconciliation Dialogue to re-engage the Alliance of Sahel States (AES) members within the continental security framework, decoupling security reintegration from immediate political conditionalities. The purpose is to close the geopolitical vacuum that enables external powers to exploit regional fragmentation. Given that AES states have explicitly rejected AU mediation, it remains to be seen what leverage the AU has.
All said and done, it is worth acknowledging that while these obstacles are pertinent, they do not negate the recommendations’ validity.
References
Official Government & Military Statements
U.S. Africa Command (AFRICOM). (2025, December 25). U.S. Africa Command conducts strike against ISIS in Nigeria. [Press Release]. https://www.africom.mil/pressrelease/36158/us-africa-command-conducts-strike-against-isis-in-nigeria
U.S. Commission on International Religious Freedom (USCIRF). (2025, November 3). Naming of Nigeria as a Country of Particular Concern is an important step to advance religious freedom. [Press Release]. https://www.uscirf.gov/news-room/releases-statements/naming-nigeria-country-particular-concern-important-step-advance
U.S. Department of Defence & Ministry of National Defence of Niger. (2024, August 5). Joint statement on the completion of withdrawal of U.S. forces and assets from Air Base 201 in Agadez. https://www.war.gov/News/Releases/Release/Article/3861097/joint-statement-from-the-us-department-of-defense-and-the-department-of-nationa/
U.S. Department of State. (2025, October 30). 2025 Redesignation of Countries of Particular Concern for religious freedom. [Official Statement].
U.S. Department of War. (2025, December 25). Statement from Secretary Hegseth on precision strikes in Nigeria. [Official Communication].
African Union Peace and Security Council. (2016, May 30). Communiqué of the 601st meeting of the PSC on the establishment of foreign military bases in Africa. (PSC/PR/COMM.(DCI). https://www.peaceau.org/en/article/communique-of-the-601st-meeting-of-the-peace-and-security-council
News & Investigative Reports
CBS News. (2025, December 26). U.S. launches strikes on ISIS targets in Nigeria on Christmas Day, Trump says. https://www.cbsnews.com/news/u-s-launches-strikes-on-isis-targets-in-nigeria-trump-says/
Business Insider Africa. (2025, May 18). U.S. moves closer to establishing its drone base in West African country. https://africa.businessinsider.com/local/lifestyle/us-moves-closer-to-establishing-its-drone-base-in-west-african-country/xld76wd
Weiss, C. (2025, December 26). U.S. strikes Islamic State in Nigeria. FDD’s Long War Journal. https://www.longwarjournal.org/archives/2025/12/us-strikes-islamic-state-in-nigeria.php
The Times of Israel. (2025, December 26). Trump says U.S. struck ISIS targets in Nigeria after group targeted Christians. https://www.timesofisrael.com/trump-says-us-struck-isis-targets-in-nigeria-after-group-targeted-christians/
Think Tank & Policy Analysis
Centre for Strategic and International Studies (CSIS). (2025, November 20). President Trump’s redesignation of Nigeria as a “Country of Particular Concern—CPC”: A serious, well-founded wake-up call. https://www.csis.org/analysis/president-trumps-redesignation-nigeria-country-particular-concern-cpc-serious-well-founded
Thurston, A. (2024, January 10). Is that U.S. drone base in Niger really necessary? Responsible Statecraft. https://responsiblestatecraft.org/us-niger-drone-base/
The Tricontinental: Institute for Social Research. (2021, July 6). Defending our sovereignty: U.S. military bases in Africa and the future of African unity (Dossier No. 42). https://thetricontinental.org/dossier-42-militarisation-africa/
Threat Assessment Sources
Armed Conflict Location & Event Data Project (ACLED). (2024). Political violence in the Nigeria-Niger-Benin border region [Data file]. https://acleddata.com/
Barnett, J. (2024). Lakurawa and the Islamic State’s expansion in north-west Nigeria. Hudson Institute. https://www.hudson.org/
Mahmoud, Y. (2025). The Sahel-Nigeria conflict convergence: JNIM and ISSP in the tri-border region. African Arguments. https://africanarguments.org/
Pérouse de Montclos, M.-A. (2025). Islamic State expansion along the Niger-Nigeria border: From banditry to jihadism. Institute for Security Studies. https://issafrica.org/
Raineri, L., & Rossi, A. (2025). The governance dimensions of insurgency in north-west Nigeria. West Africa Report, 12(3), 45-67.
Zenn, J. (2024). Islamic State Sahel Province: Operational evolution and strategic objectives in West Africa. Jamestown Foundation Terrorism Monitor, 22(24), 12-18.
Drone Capabilities & Ecosystems
Baykar Technologies. (n.d.). Bayraktar TB2 tactical UAS. https://baykartech.com/en/uav/bayraktar-tb2/
International Institute for Strategic Studies. (2023). The Military Balance 2023. Routledge. https://www.iiss.org/publications/the-military-balance
Jane’s Defence Weekly. (2022). Nigeria expands UAV inventory with Turkish systems. https://www.janes.com/
Military Africa. (2024). Nigeria’s drone inventory: From CH-3A to indigenous attack UAVs. https://www.military.africa/2025/12/us-launches-airstrike-against-isis-networks-in-northwest-nigeria/
Textron Systems. (n.d.). Aerosonde UAS. https://www.textronsystems.com/products/aerosonde
U.S. Department of Defence. (2021). Contract announcements: Aerosonde systems for partner nations. https://www.defense.gov/News/Contracts/
General Atomics Aeronautical Systems. (2024). MQ-9B SkyGuardian/SeaGuardian: The next generation of Remotely Piloted Aircraft Systems. https://www.ga-asi.com/remotely-piloted-aircraft/mq-9b
Commentary
Ghana’s AI Strategy is more than a policy, it is a declaration of digital sovereignty
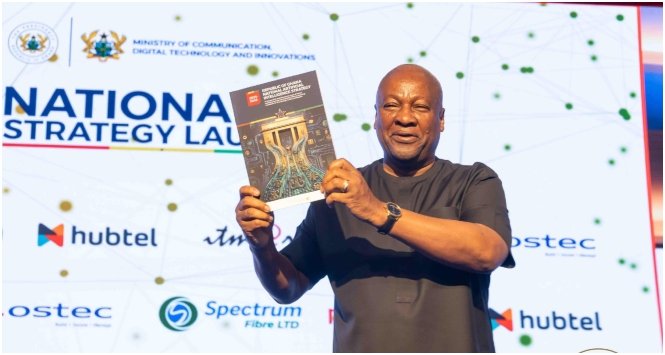
In this feature commentary, George Spencer Quaye argues that Ghana’s newly launched National AI Strategy represents far more than a routine policy document; it is a deliberate “declaration of digital sovereignty” aimed at repositioning Africa from a consumer of foreign technologies to a builder and owner of intelligent systems.
Ghana’s AI Strategy is more than a policy, it is a declaration of digital sovereignty
By George Spencer Quaye
Last Friday, in Accra, Ghana did more than launch a strategy.
Under the leadership of H.E. President John Dramani Mahama, and through the stewardship of the Minister for Communications, Digital Technology and Innovation, Samuel Nartey George, the country issued what must be understood for what it truly is:
A declaration of digital sovereignty in the age of artificial intelligence.
At a time when global power is increasingly defined not by territory or raw resources, but by control over data, algorithms, and compute infrastructure, Ghana has made a strategic choice—to compete, to lead, and crucially, to own its place in the emerging AI order.
This is not a symbolic move. It is a political one.
The Politics of Intelligence
Artificial intelligence is often framed as a technological revolution. That framing is incomplete.
AI is about power.
It determines:
- Who controls knowledge
- Who shapes economic value
- Who defines truth in digital systems
- And ultimately, who governs the future
For too long, Africa has sat at the receiving end of global technological systems—importing platforms, exporting raw data, and absorbing outcomes shaped elsewhere.
That model is no longer sustainable.
Ghana’s National AI Strategy confronts this reality head-on. By committing to sovereign AI infrastructure, investing in local innovation ecosystems, and proposing governance institutions to regulate the deployment of intelligent systems, the government is signaling a break from dependency.
It is asserting that Africa must not only participate in the AI revolution—but must negotiate its terms.
From Digital Dependence to Digital Control
The implications of this shift are profound.
A National AI Computing Centre is not just infrastructure—it is strategic autonomy.
An AI Fund is not just financing—it is control over innovation direction.
A Responsible AI Authority is not just regulation—it is protection against digital subjugation.
Taken together, these moves represent an attempt to reposition Ghana—and by extension Africa—from the periphery of the digital economy to its commanding heights.
In the AI era, those commanding heights are no longer mines or oil fields.
They are data centres, algorithms, and digital infrastructure.
A Continental Imperative
Ghana’s move must not remain a national story.
It must become a continental turning point.
Because the reality is stark: if African countries do not build sovereign AI capabilities, they risk entering a new era of digital colonialism—one where decisions about African economies, societies, and governance are increasingly mediated by foreign-owned intelligent systems.
This is not alarmism. It is already happening.
From financial algorithms to content moderation systems, from credit scoring to predictive analytics, Africa is being modeled, interpreted, and influenced by systems it does not control.
Ghana’s strategy is therefore not just timely—it is necessary.
But it cannot stand alone.
From Strategy to Doctrine: The Role of MOBEX Africa
At MOBEX Africa, we view this moment as pivotal.
Our theme—“Resetting Africa’s Digital Identity and Sovereignty; From Promise to Practice”—was conceived around the recognition that Africa must move from digital participation to digital control.
The launch of Ghana’s AI Strategy validates that thesis.
But validation is not enough. What is required now is coordination, alignment, and execution at scale.
At the upcoming MOBEX Africa Tech Innovation Conference, we will:
- Interrogate national AI strategies and their readiness for implementation
- Convene policymakers, regulators, and industry leaders to define governance frameworks
- Showcase real-world applications of AI in public systems
- Advance the development of an Accra Declaration on AI Sovereignty
The Test Ahead
Commendation is deserved.
The leadership shown by President Mahama, Minister Sam George, and the Government of Ghana in taking this bold, forward-looking step must be acknowledged.
But strategy is only the beginning.
The real challenge lies ahead:
- Can Ghana build and sustain world-class AI infrastructure?
- Can it develop and retain the talent required to power it?
- Can it regulate effectively without stifling innovation?
- Can it bring the private sector along as a true partner?
These questions will determine whether this moment becomes a milestone—or a missed opportunity.
A Moment That Must Define a Generation
Africa stands at a crossroads.
One path leads to continued dependence—where the continent consumes technologies it neither owns nor controls.
The other leads to sovereignty—where Africa builds, governs, and benefits from its own intelligent systems.
Ghana has chosen the latter.
Now the task is to ensure that choice is not isolated, but replicated, scaled, and sustained across the continent.
Because in the age of artificial intelligence, sovereignty will not be declared in speeches.
It will be built in systems.
About the author
George Spencer Quaye is the founder and Chief Executive Officer of MOBEX Africa. He is a governance and digital transformation strategist, public policy commentator and board-level leader. He writes on leadership, political reform and Africa’s development trajectory. He’s currently serving as the Chairman of the Governing Board of the Driver and Vehicle Licensing Authority.
Opinion
Surrogacy in Ghana: Legal parenthood, registration, and the rights of the surrogate

Ghana’s legal framework for surrogacy has evolved with the passage of the Registration of Births and Deaths Act, 2020 (Act 1027), which, for the first time, provides statutory recognition and a mechanism, through High Court parental orders, for regularizing parentage in assisted reproductive arrangements. However, in this article by Joseph Ackah-Blay argues that while this represents progress, Ghana still lacks a coherent and comprehensive legal regime for surrogacy.
Surrogacy in Ghana: Legal parenthood, registration, and the rights of the surrogate
By Joseph Ackah-Blay, Esq.
Surrogacy is no longer a novelty in Ghana. More families are turning to it. More clinics are facilitating it. More lawyers are being asked to structure it. The law, for its part, has started to respond. But only just. It is no longer entirely correct to say Ghana has no law on surrogacy. That position, while once accurate, no longer reflects the statutory landscape. Yet it would be equally wrong to suggest that Ghana now has a coherent and comprehensive legal regime governing assisted reproduction. It does not. What we have instead is something in between: statutory recognition without full regulation; legislative movement without complete legislative architecture.
That framework is found principally in the Registration of Births and Deaths Act, 2020 (Act 1027). Through it, Parliament has for the first time given express statutory recognition to assisted reproductive births and created a mechanism through which parentage arising from surrogacy may be regularised. That is progress. But progress and completion are not the same thing.
The Constitutional Framework
The 1992 Constitution says nothing directly about surrogacy. That is hardly surprising. The Constitution predates the modern fertility industry and was never drafted with assisted reproductive technology in mind. Still, constitutional principles remain relevant.
Article 15(1) provides that: “The dignity of all persons shall be inviolable.”
That matters. It places constitutional limits on how surrogate mothers may be treated, what may be demanded of them, and how far contractual arrangements may go. The Constitution also speaks to the welfare of children. Article 28(1)(a) requires legislative protection for children, while section 2 of the Children’s Act, 1998 (Act 560) reiterates the settled principle that the best interests of the child shall be paramount in any matter concerning a child. These principles will almost certainly frame any judicial consideration of a surrogacy dispute if and when one comes before the courts.
What the Law Now Provides
The centrepiece of Ghana’s present surrogacy framework is section 22 of Act 1027. It creates a statutory process through which intended parents and surrogate mothers may apply to the High Court for orders relating to legal parentage in assisted reproductive arrangements. The provision contemplates both pre-birth and post-birth applications.
Under section 22(2), an intended parent may apply within twelve weeks after the introduction of the embryo or gamete into the surrogate for what is, in substance, a pre-birth parental order. If satisfied as to the evidence of parentage and the existence of the surrogacy arrangement, the High Court may direct that the intended parent, the surrogate, or both be named as the legal parent or parents of the child. This requirement kicks in if the birth occurs within twenty-eight weeks of the order.
Where no such order is obtained before birth, the Act permits a further application after birth for a parental or substitute parentage order, upon which the Court may direct the registration or re-registration of the child’s birth accordingly. This post-birth order must be requested for earlier than twenty-eight days after birth and not later than six months after birth. Such an order is treated in the form of an adoption proceeding. An important point worth noting is that where a substitute parentage order is granted, the original birth record is struck out, sealed and kept confidential, and the child gains a right to access it at the age of twenty-one.
Without such an order, the default statutory position is plain enough: the woman who gives birth is to be registered as the mother of the child. That is no small development. It is the first serious legislative acknowledgment that surrogacy exists within Ghanaian family life and requires legal accommodation. But this acknowledgment is not clarity. The courts have not yet had much opportunity to develop jurisprudence on section 22. How precisely the provision will operate in contested or difficult cases remains to be seen.
The Contract Matters
Surrogacy arrangements are typically reduced into writing between intended parents and the surrogate. That is prudent. Indeed, it is essential. Such agreements usually address parentage, medical care, compensation, confidentiality, and consent to subsequent legal processes. Still, a surrogacy agreement should not be mistaken for a complete legal solution. It may record intention. It may regulate expectations. It may provide evidence. But no Ghanaian statute presently provides that such an agreement, by itself, conclusively determines legal parentage. Nor have the courts definitively pronounced on the extent to which such agreements may be enforced in the event of dispute. The contract is important. It simply is not everything.
When the Surrogate Is Married
Things become more complicated where the surrogate is married. Under section 32 of the Evidence Act, 1975 (N.R.C.D. 323), a child born during a marriage is presumed to be the child of the husband of the mother. The presumption is rebuttable. But unless rebutted, it remains the legal starting point. Its practical implication is obvious enough: where a married surrogate carries a child, her husband may presumptively occupy the position of legal father unless the appropriate legal and evidential steps are taken to establish otherwise. That is one reason lawyers may advise on the husband’s participation in the relevant documentation and legal process where applicable.
What of Adoption?
Before Act 1027, adoption was commonly used in practice to regularize parentage after surrogacy arrangements. Whether that remains necessary in every case is no longer entirely clear. Section 22 of ACT 1027 has changed the landscape. To what extent it has displaced adoption as the principal route to legal parenthood in surrogacy matters is a question the courts are yet to answer with any real precision. For now, the relationship between the parental-order mechanism under Act 1027 and the adoption framework under the Children’s Act remains a developing one.
The Surrogate Is Not Merely a Vessel
In public discourse, discussions of surrogacy often focus almost entirely on intended parents. The surrogate is treated as incidental to the arrangement. Legally, she is not. She remains a rights-bearing actor throughout the process. She retains bodily autonomy. No law authorises intended parents to compel her to undergo treatment, submit to procedures, or make reproductive decisions against her will. She retains dignity protections under Article 15(1). And until the statutory process under Act 1027 is completed, the precise contours of her legal position remain, in several respects, underdeveloped in Ghanaian jurisprudence. That uncertainty is not merely theoretical. It has practical implications for everyone involved.
Outstanding Work
Act 1027 is a meaningful beginning. It is not a finished framework. Other jurisdictions have gone considerably further. South Africa, for example, requires judicial confirmation of surrogate motherhood agreements before conception under Chapter 19 of its Children’s Act 38 of 2005.
The United Kingdom provides a dedicated parental-order regime under section 54 of the Human Fertilisation and Embryology Act 2008. Ghana, by contrast, still lacks a dedicated assisted reproduction statute, detailed procedural rules for surrogacy applications, and developed jurisprudence on the operation of its existing provisions.
The law has begun to speak. It has not yet said enough.
Conclusion
Surrogacy now sits within Ghana’s statutory framework. That much is clear. What remains less clear is how far that framework goes, how the courts will interpret it, and whether it is sufficient for the realities of a growing assisted reproduction industry. Act 1027 has moved the law forward. It has not completed the journey. Until the courts provide fuller guidance or Parliament enacts a more comprehensive legislative scheme, surrogacy in Ghana will remain an area of legal recognition attended by legal uncertainty. And where the law is uncertain, caution is not optional. It is essential.
Joseph Ackah-Blay is an Associate at Renaissance Law Chambers, where he advises on corporate, commercial, regulatory, IT law and private legal matters. He writes generally on law, governance, and emerging legal issues. He holds a B.A., LL.B and QCL. He can be reached at j.ackahblay74@gmail.com
Perspectives
Leased Sovereignty: Ghana, the EU, Ukraine and the Politics of Security Dependency

In March 2026, Ghana became the first African nation to sign a Security and Defence Partnership (SDP) with the European Union, while simultaneously negotiating a Defence Cooperation Agreement (DCA) with Ukraine.
This strategicpolicy analysis report by the renowned security expertCol. Festus Aboagye (retd) examines both agreements, arguing that the central question is not whether Ghana should have signed them, the strategic logic is compelling, but whether Ghana has the institutional architecture to translate external partnerships into sovereign capability rather than structural dependency.
The report introduces the concept of “leased sovereignty” to describe a condition in which a state formally owns military capabilities but does not control them, because maintenance, software architecture, data infrastructure, and supply chains all remain with the provider.
Drawing on documentary analysis of primary official sources, secondary institutional research, and forthcoming primary research from a 15‑state African study on data sovereignty in third‑party defence grants, the analysis identifies five structural risks: interoperability fragmentation, border surveillance governance gaps, narrative incoherence between Ghana’s pan‑African moral leadership and its new EU security role, intelligence data sovereignty exposure, and supply‑chain fragility inherent in a technology relationship with a nation at active war.
The report concludes with a three‑horizon implementation roadmap sequencing the institutional, legal, and operational measures required to convert dependency into enduring national capability.
It argues that Ghana’s 2026 agreements are a test case for whether an African middle power can engage Global North security frameworks on its own terms—acquiring capability without conceding control, anchoring regional stability without subordinating sovereignty, and transforming a bilateral diplomatic achievement into a continental governance precedent.
Click here to access the full 24-page report.
-

 Ghana News1 day ago
Ghana News1 day agoNewspaper Headlines Today: Thursday, April 30, 2026
-

 Business1 day ago
Business1 day agoJet Fuel Crunch Fears Ease for Ghana, But Global Supply Questions Remain
-

 Ghana News2 days ago
Ghana News2 days agoWhy Ghana Walked Away From $109 Million US Health Package
-

 Business1 day ago
Business1 day agoGovernment of Ghana Issues Formal Call for Investors to Establish Airline by First Quarter 2027
-

 Ghana News1 day ago
Ghana News1 day agoNo Ghanaian Killed in South Africa Xenophobic Attacks, Arrests Made in Missing Couple Case, and Other Big Stories in Ghana
-

 Ghana News1 day ago
Ghana News1 day agoGhana Expresses Solidarity With Mali After Terrorist Attacks
-

 Ghana News1 day ago
Ghana News1 day agoMahama Under Pressure Over Attacks on Ghanaians in South Africa: Minority MPs Demand Direct Presidental Engagement
-

 Arts and GH Heritage1 day ago
Arts and GH Heritage1 day agoGhana’s Art Boom at Risk Without State Investment, Experts Warn







